
A macOS version of the LightSpy surveillance framework has been discovered, confirming the extensive reach of a tool only previously known for targeting Android and iOS devices.
LightSpy is a modular iOS and Android surveillance framework used to steal a wide variety of data from people’s mobile devices, including files, screenshots, location data (including building floor numbers), voice recordings during WeChat calls, and payment information from WeChat Pay, and data exfiltration from Telegram and QQ Messenger.
The attackers behind the framework use it in attacks against targets in the Asia–Pacific region.
According to a new report by ThreatFabric, a macOS implant has been discovered to be active in the wild since at least January 2024. However, its operation appears to be currently limited to testing environments, and a handful of infected machines are used by cybersecurity researchers.
The researchers infiltrated LightSpy’s control panel by exploiting a misconfiguration that allowed unauthorized access to the authenticated interface, gaining insights into the functionality, infrastructure, and infected devices.
Using exploits to compromise macOS
The threat actors use WebKit flaws CVE-2018-4233 and CVE-2018-4404 to trigger code execution within Safari, targeting macOS 10.13.3 and earlier.
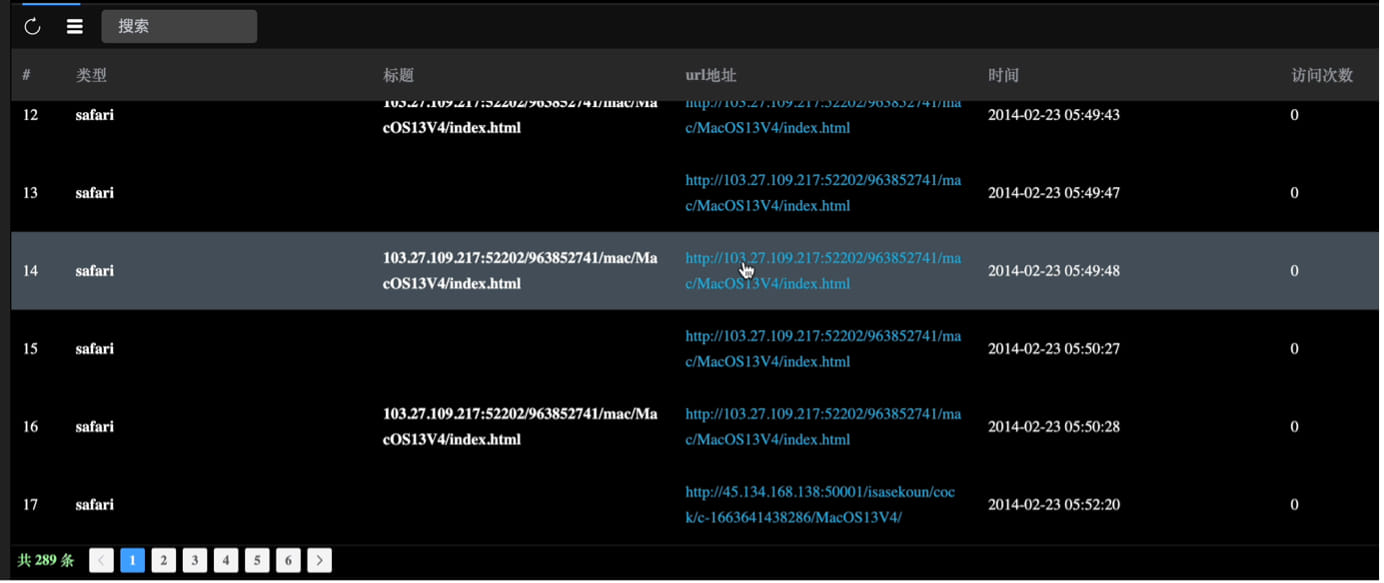
Source: ThreatFabric
Initially, a 64-bit MachO binary disguised as a PNG image file (“20004312341.png”) is delivered on the device, decrypting and executing embedded scripts that fetch the second stage.
The second stage payload downloads a privilege escalation exploit (“ssudo”), an encryption/decryption utility (“ddss”), and a ZIP archive (“mac.zip”) containing two executables (“update” and “update.plist”).
Eventually, the shell script decrypts and unpacks these files, gaining root access on the breached device and establishing persistence on the system by configuring the “update” binary to run at startup.
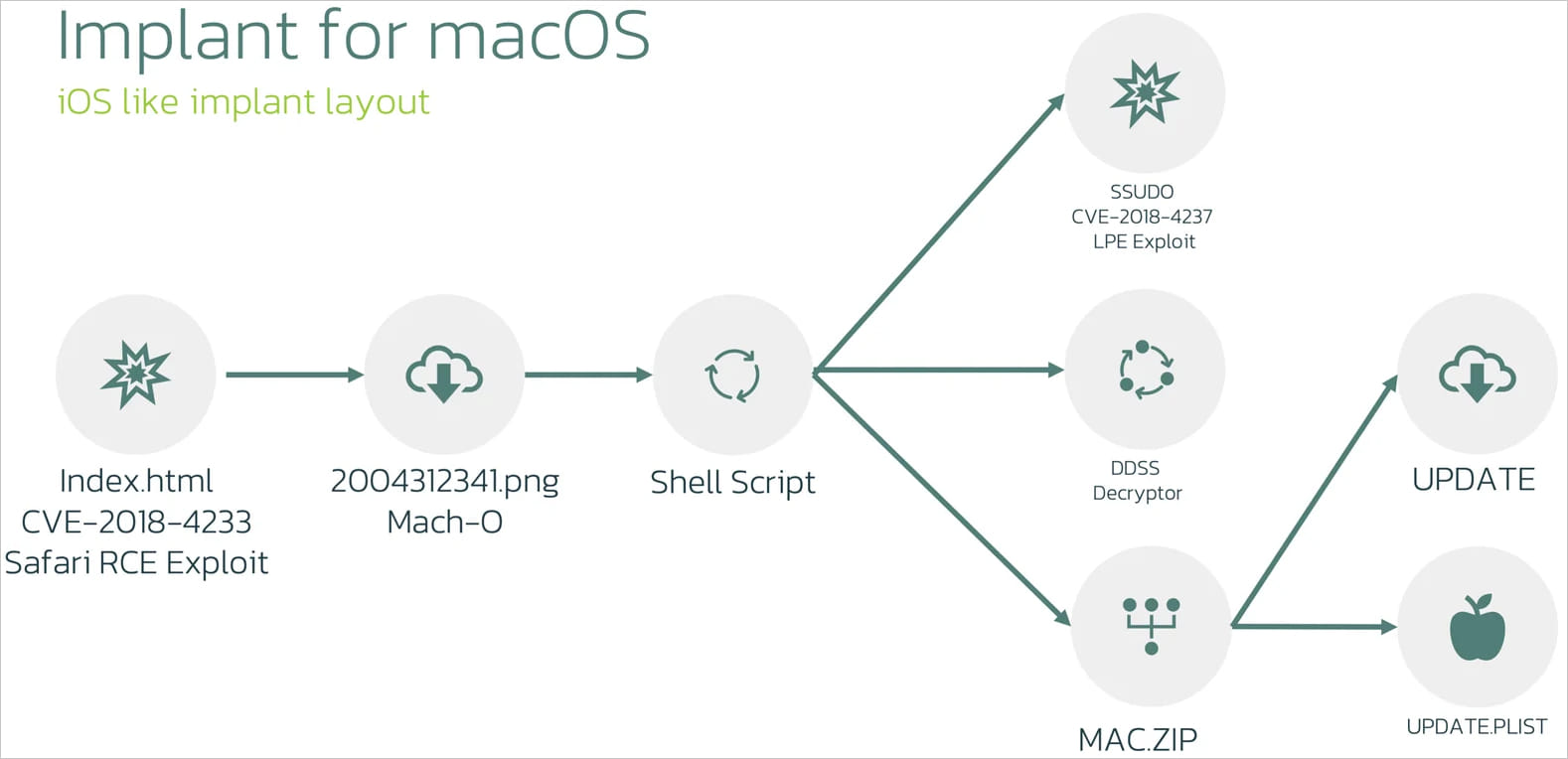
Source: ThreatFabric
The next step is carried out by a component called “macircloader,” which downloads, decrypts, and executes LightSpy Core.
This acts as the central plugin management system for the spyware framework and is responsible for communications with the command and control (C2) server.
LightSpy core can also execute shell commands on the device, update its network configuration, and set an activity timetable to evade detection.
LightSpy plugins
The LightSpy framework extends its spying functionality using various plugins that perform specific actions on the compromised device.
Though the malware uses 14 plugins on Android and 16 plugins on its iOS implant, the macOS version uses the following ten:
- soundrecord: Captures sound from the microphone.
- browser: Extracts browsing data from popular web browsers.
- cameramodule: Takes photos using the device’s camera.
- FileManage: Manages and exfiltrates files, especially from messaging apps.
- keychain: Retrieves sensitive information stored in the macOS Keychain.
- LanDevices: Identifies and gathers information about devices on the same local network.
- softlist: Lists installed applications and running processes.
- ScreenRecorder: Records the device’s screen activity.
- ShellCommand: Executes shell commands on the infected device.
- wifi: Collects data on Wi-Fi networks the device is connected to.
These plugins enable LightSpy to perform comprehensive data exfiltration from infected macOS systems, while its modular design gives it operational flexibility.
ThreatFabric notes in its report that their access to the attacker’s panel confirmed that implants for Windows, Linux, and routers exist but could not determine how they are used in attacks.
“Despite our findings, some aspects of the LightSpy puzzle remain elusive,” concludes ThreatFabric.
“There is no evidence confirming the existence of implants for Linux and routers, nor is there information on how they might be delivered. However, their potential functionality is known based on panel analysis.”




Comments