
Check Point has released hotfixes for a VPN zero-day vulnerability exploited in attacks to gain remote access to firewalls and attempt to breach corporate networks.
On Monday, the company first warned about a spike in attacks targeting VPN devices, sharing recommendations on how admins can protect their devices. Later, it discovered the source of the problem, a zero-day flaw that hackers exploited against its customers.
Tracked as CVE-2024-24919, the high-severity information disclosure vulnerability enables attackers to read certain information on internet-exposed Check Point Security Gateways with remote Access VPN or Mobile Access Software Blades enabled.
“The vulnerability potentially allows an attacker to read certain information on Internet-connected Gateways with remote access VPN or mobile access enabled,” reads an update on Check Point’s previous advisory.
“The attempts we’ve seen so far, as previously alerted on May 27, focus on remote access scenarios with old local accounts with unrecommended password-only authentication.”
CVE-2024-24929 impacts CloudGuard Network, Quantum Maestro, Quantum Scalable Chassis, Quantum Security Gateways, and Quantum Spark Appliances, in the product versions: R80.20.x, R80.20SP (EOL), R80.40 (EOL), R81, R81.10, R81.10.x, and R81.20.
Check Point has released the following security updates to address the flaw:
- Quantum Security Gateway and CloudGuard Network Security: R81.20, R81.10, R81, R80.40
- Quantum Maestro and Quantum Scalable Chassis: R81.20, R81.10, R80.40, R80.30SP, R80.20SP
- Quantum Spark Gateways: R81.10.x, R80.20.x, R77.20.x
To apply the update, head to the Security Gateway portal > Software Updates > Available Updates > Hotfix Updates, and click ‘Install.’
The vendor says the process should take approximately 10 minutes, and a reboot is required.
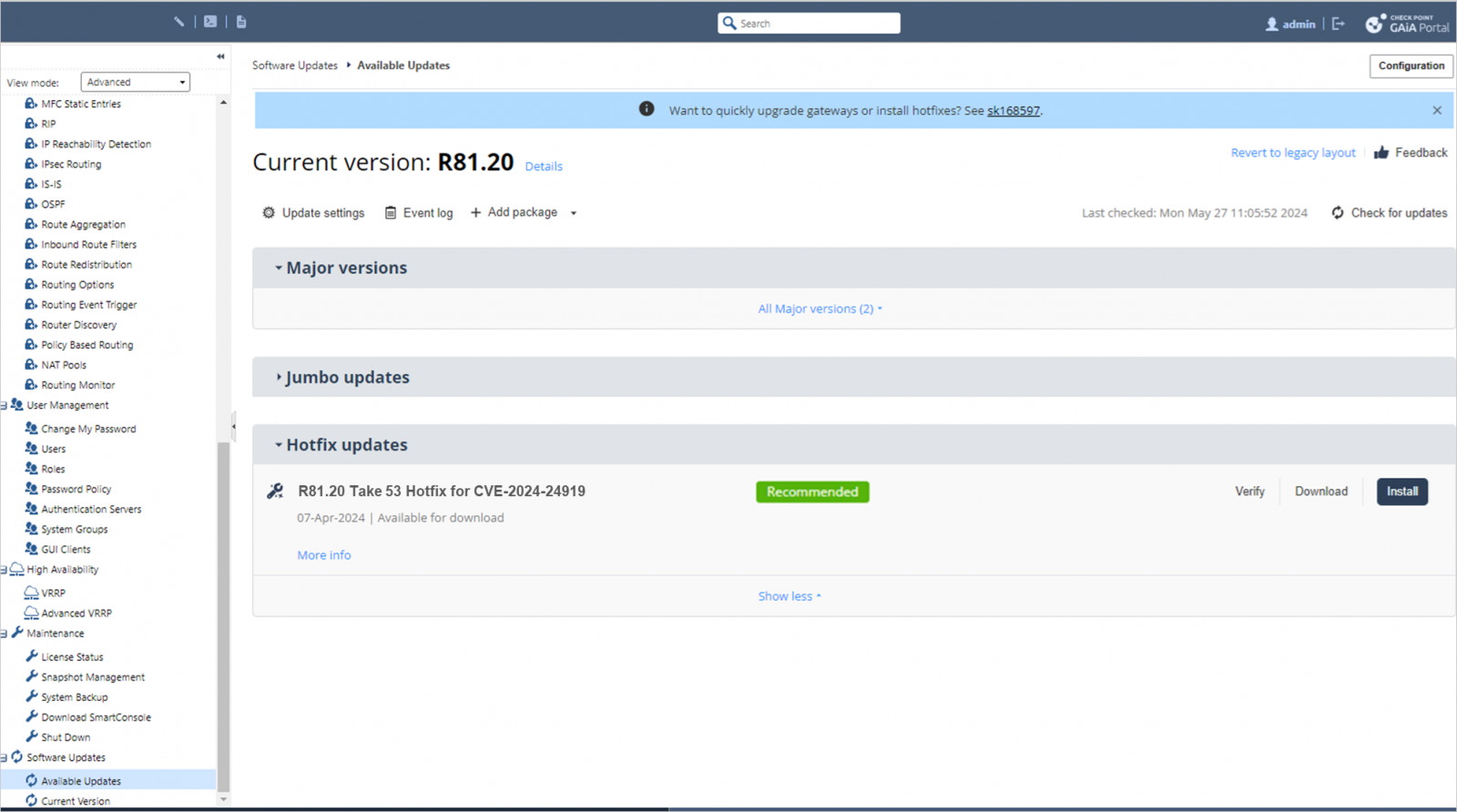
Source: Check Point
After the hotfix is installed, login attempts using weak credentials and authentication methods will be automatically blocked, and a log will be created.
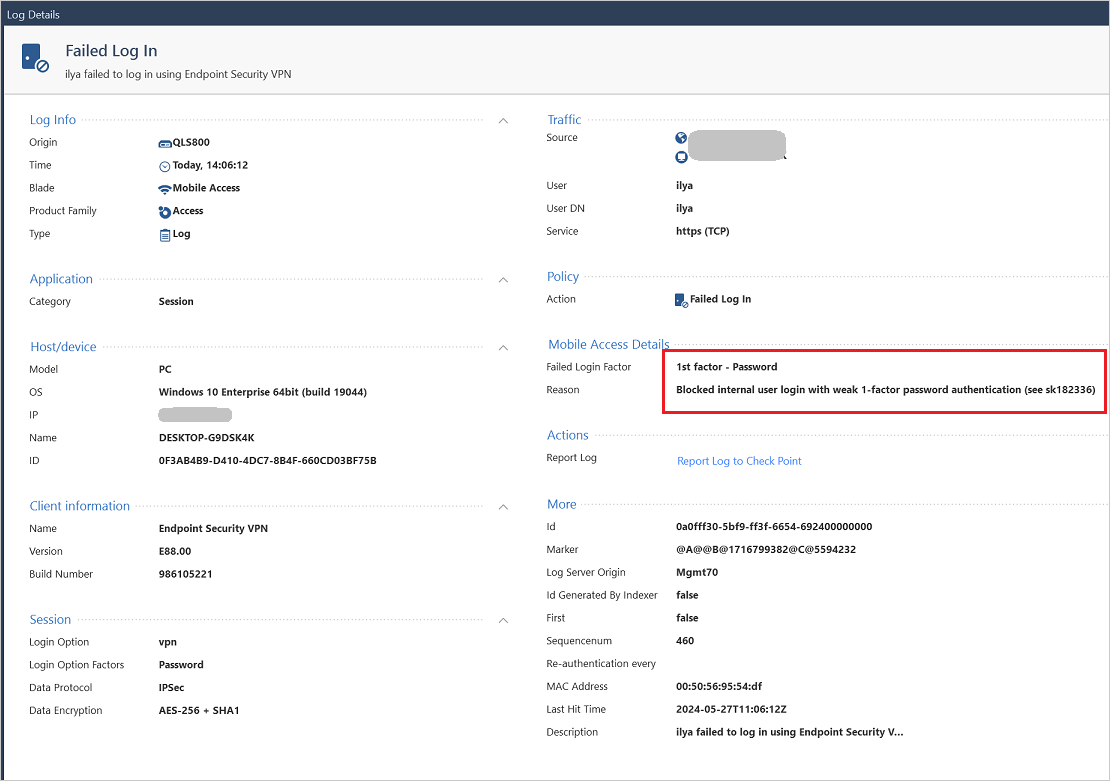
Source: Check Point
Hotfixes have been made available for end-of-life (EOL) versions, too, but they must be downloaded and applied manually.
Check Point created a FAQ page with additional information about CVE-2024-24919, IPS signature, and manual hotfix installation instructions.
Those unable to apply the update are advised to enhance their security stance by updating the Active Directory (AD) password that the Security Gateway uses for authentication.
Additionally, Check Point has created a remote access validation script that can be uploaded onto ‘SmartConsole’ and executed to review the results and take appropriate actions.
More information on updating the AD password and using the ‘VPNcheck.sh’ script are available on Check Point’s security bulletin.




Comments